The Challenge
Security incidents happen at some point. It's a fact of life. Through Security Colony, you now possess the resources to help you close the gap that exists between your current approach to dealing with security incidents and having a great plan when an incident occurs.
Resources Available to Free Users
Through your free Security Colony account you have access to a range of resources that you can use to build an incident response capability.
- High level incident response plan - Walks you through the basics that every organisation needs to consider before an incident, and to help ensure you ask the right questions during an incident.
- Cyber Security Contacts - To effectively respond to an incident, a list of cyber security contacts should be maintained. This is a key document identifying the key cyber security authorities (i.e. law enforcement, CERTS and other groups) that may be required in the event of a cyber security incident in the Australian market and is a requirement under the ISO 27001 standard.
- Breach Notification Letter - This is a simple letter you can use in the unfortunate event that you need to let your customers know that a data breach has occurred.
In case you're starting from a blank page, the documents above will get you started and after adopting them you'll be in a much better position than you were earlier.
Resources Available to Premium Users
Security Colony paid subscribers also get access to additional documents and tools to establish an enterprise grade incident response plan. These resources have been listed below
- Breach Intelligence & Breach Monitor - Full access to run searches across our Breach Database, and set up stored searches in our Breach Monitor system. Scraping thousands of new entries every day from dump sites across the Internet, you find out potential breaches earlier, and respond faster.
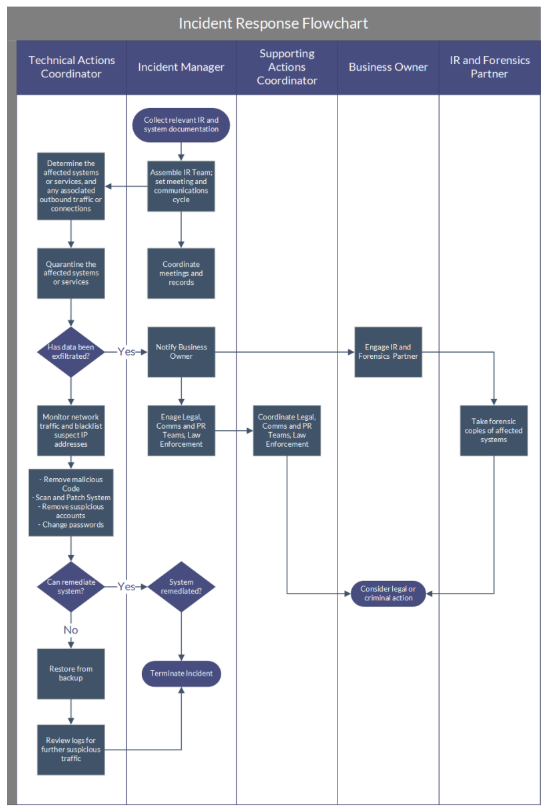
- Incident Response Guide - Document providing a reference to assist with the conduct of incident response activities including helpful hints based on our experience. This document refers to other resources which may be useful throughout the course of the incident to ensure all incident management activities are completed, and the best outcomes achieved.
- Incident Management Standard - Covers the entire incident response cycle including the incident preparation, monitoring & reporting, analysis & escalation, handling and review phases and sets out the rules for timely and effective handling of IT security incidents throughout an organisation.
- Incident Response Communication Plan Requirements - Covers the key elements needed to develop a communications plan as part of an incident response strategy.
- Incident Response Run Sheets - High-level reference guides for responding to specific attack types (DoS Attack, Phishing, Network Breach and Website Defacement) aimed at your organisation, along with key hints to ensure the thoroughness of your response.
Other Security Colony Features That Can Help
If you have any further questions about establishing an incident response system, you can get in touch with us via the "Ask a Consultant" function.
Paid subscribers also have their own Private Forum dedicated to their organisation.
Questions from free users will be answered when we can fit them in (but it generally won't take long).